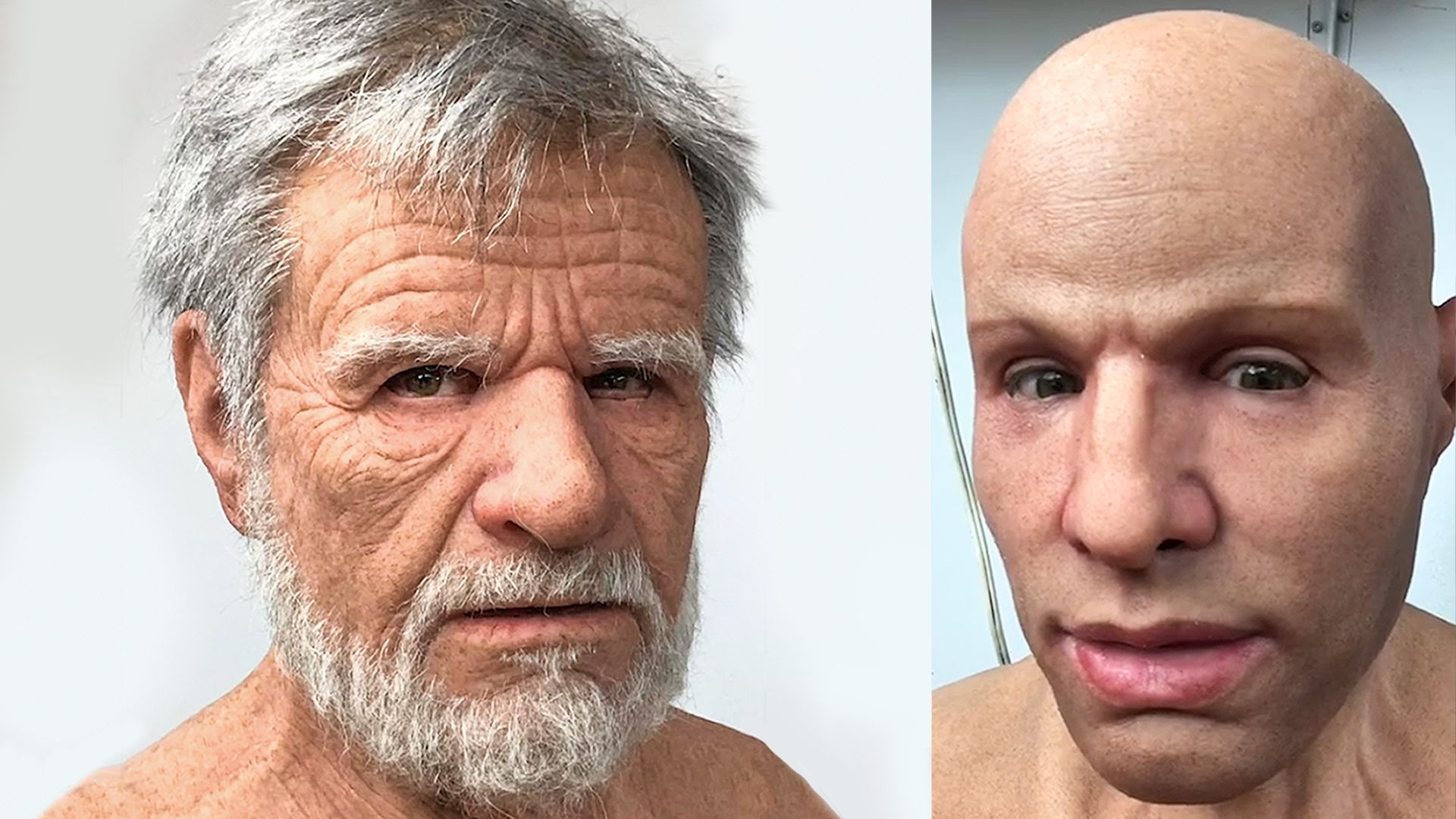
Hyper-realistic silicone masks: a new challenge in person identification
Conceptual
We frequently recognize individuals utilizing face pictures. This is valid in word related settings, for example, visa control as well as in ordinary social conditions. Planning among pictures and personalities expects that facial appearance is steady inside specific limits. For instance, an individual’s evident age, orientation and identity change gradually, if by any stretch of the imagination. It additionally accepts that intentional changes past these limits (i.e., Realistic Halloween mask) would be not difficult to recognize. Hyper-reasonable facial coverings upset these suppositions by permitting the wearer to seem to be a completely unique individual.
If inconspicuous, these covers break the connection between facial appearance and individual character, with clear ramifications for applied face acknowledgment. Be that as it may, until now, nobody has evaluated the authenticity of these covers, or determined conditions under which they might be acknowledged as genuine appearances. Thus, we analyzed accidental identification of unforeseen however gone to hyper-sensible covers in both visual and live introductions. Try 1 (UK; n = 60) uncovered no proof for obvious location of hyper-practical veils among genuine face photographs, and little proof of clandestine identification.
Analyze 2 (Japan; n = 60) stretched out these discoveries to various veils, cover wearers and member pools. In Trial 3 (UK and Japan; n = 407), passers-by neglected to see that a live confederate was wearing a hyper-sensible veil and showed restricted proof of secretive identification, even at close survey distance (5 versus 20 m). Across these investigations, watchers acknowledged hyper-practical veils as genuine appearances. Explicit countermeasures will be required assuming discovery rates are to be moved along.
Importance
In a few high-profile criminal cases, guilty parties have utilized hyper-sensible facial coverings to change their appearance, driving police to seek after suspects who seem to be the actual wrongdoers (e.g., different race or age). In different settings, carrier travelers wearing hyper-reasonable veils have loaded onto global trips without the duplicity being taken note. Such episodes are probably going to turn out to be more normal as hyper-practical covers become simpler to produce. These improvements have possibly extensive ramifications for security and wrongdoing avoidance. Face distinguishing proof requires a coordinated planning among countenances and individuals, so appearance can be followed to character unambiguously. On the off chance that watchers don’t recognize hyper-sensible veils and genuine countenances, the planning can be compromised, and facial appearance is presently not educational for distinguishing proof. We find that watchers neglect to recognize hyper-reasonable veils, in any event, when they take care of facial appearance. Special cases for this example allude to potential techniques for further developing recognition execution.
FoundationFace acknowledgment is a typical method for recognizing individuals and a significant part of safety and wrongdoing counteraction universally. For instance, visa issuance (White, Kemp, Jenkins, Matheson, and Burton, 2014) and identification control (McCaffery and Burton, 2016) both include facial picture correlation. Conviction of criminal suspects can here and there rely on observer declaration (Wells and Olson, 2003; Bruce, 1988; https://www.innocenceproject.org) or CCTV film (Burton, Wilson, Cowan, and Bruce, 1999; Davis and Valentine, 2009). In numerous nations, a personal ID is expected for the acquisition old enough confined merchandise (Gosselt, van Foot, de Jong, and Prinsen, 2007; Vestlund, Langeborg, Sörqvist, and Eriksson, 2009). Since face recognizable proof conveys such weight in these circumstances, it is likewise a significant concentration for personality extortion and misdirection (Robertson, Kramer, and Burton, 2017). Specifically, people might wish to imitate another person or to try not to be perceived themselves (Dhamecha, Singh, Vatsa, and Kumar, 2014).